Tools
BGPWatch, CGTF Looking Glass, CGTF RIS, FlowWatch, Gperf.
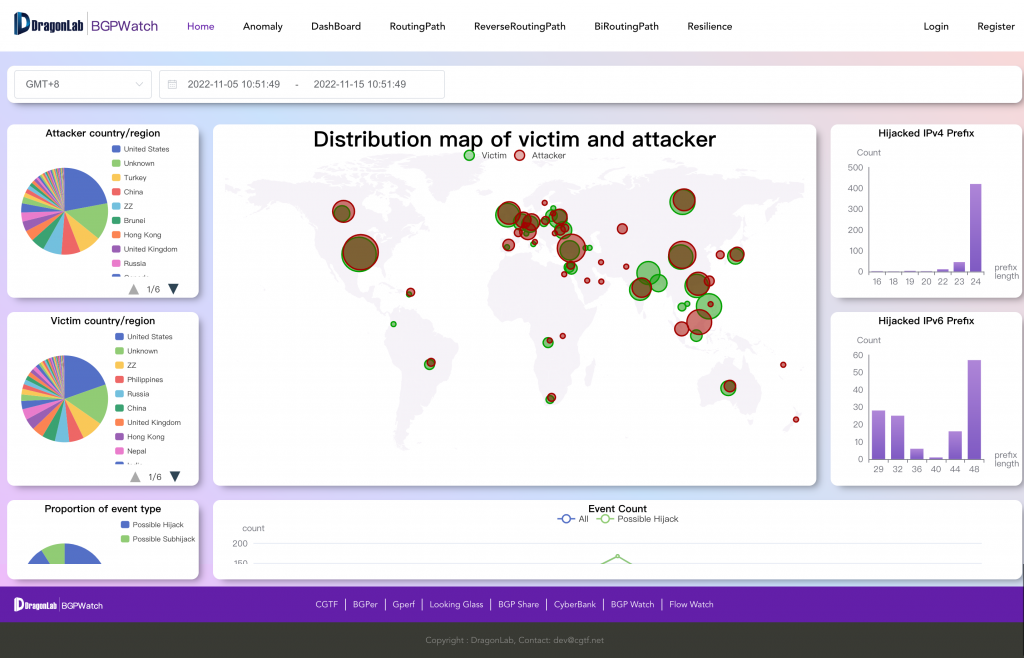
BGP is an unsecure protocol, and any AS on the Internet can forge a BGP message. This vulnerability leads to a lot of harmful BGP events all over the Internet, and BGP hijacking is the famous one. BGPWatch is a knowledge-based real-time BGP hijacking detecting system, which could help monitor the BGP hijacking happening on the Internet. It is mainly based on MOAS and subMOAS events, and relies on domain knowledge, such as ROA, IRR, AS relationship, AS topology, etc.
- url:http://bgpwatch.cgtf.net
- Knowledge-based real-tIme BGP hIjacking Detection System
- Based on MOAS (subMOAS)
- Exclude legal MOAS by using domain knowledge and rules(ROA, IRR, AS relationship, etc
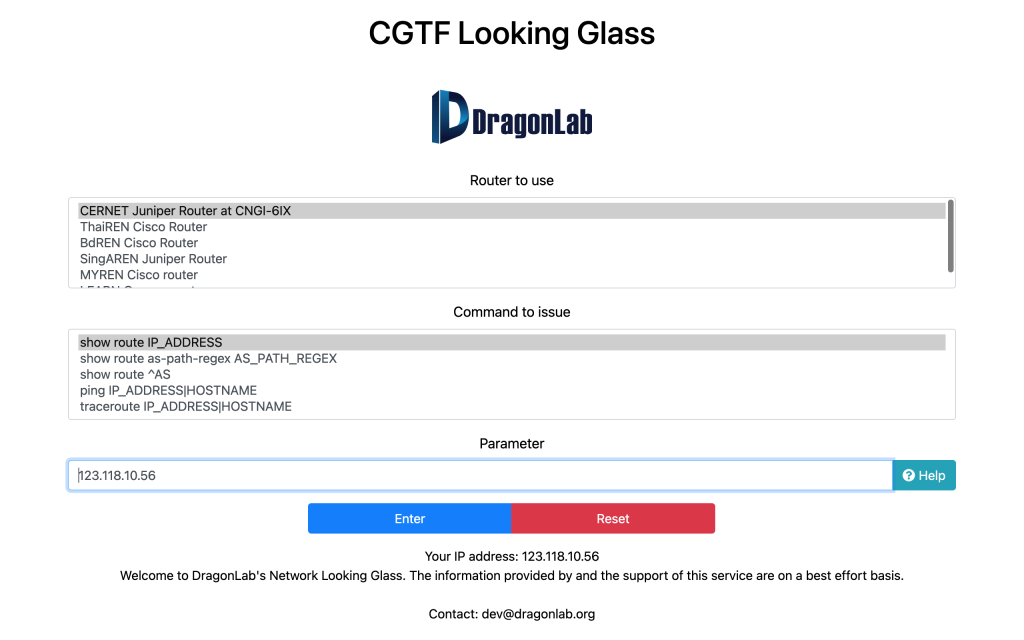
Looking Glass (LG) is a command line interface that provides users with limited access to the router. LG servers are deployed in different parts of the Internet and allow on-line checking of prefixes, collected from the BGP speaking routers. It is usually used for network diagnosis and can also provide data for scientific research. This LG server (https://lg.cgtf.net) provides access to several educational networks in Asia and supports several commands such as “ping”, “traceroute”, and “show bgp route”.
- url: https://lg.cgtf.net
- Based on open source: https://github.com/gmazoyer/looking-glass
- Set query speed limit for security
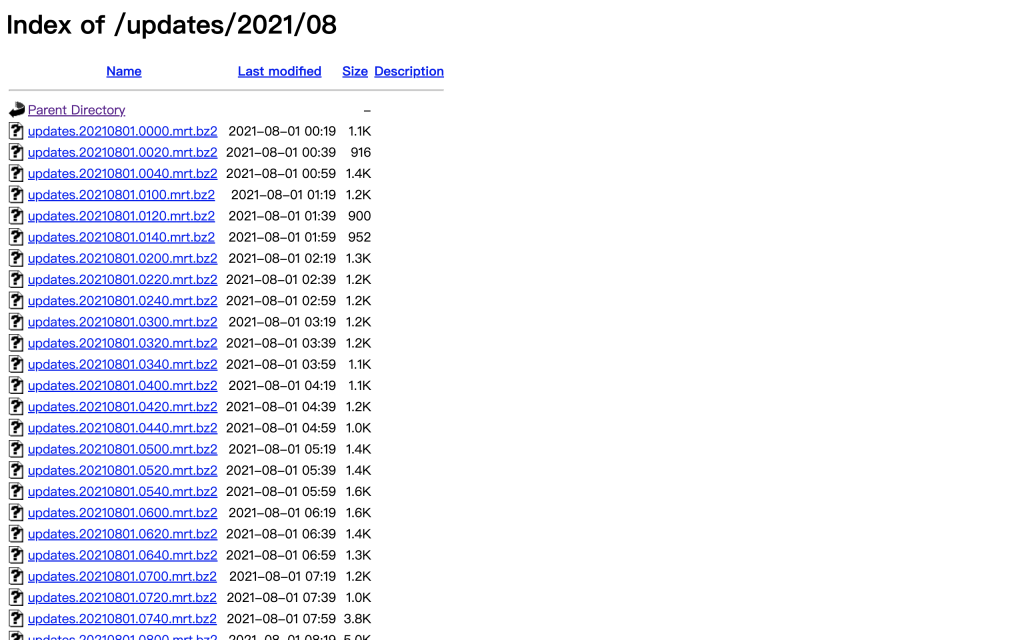
BGP route collection platforms collect and log BGP routing information observed from different ASes. These routing information can be used for network diagnosis, historical BGP event review, and scientific research etc.
- url: https://bgp.cgtf.net
- Use routing FRR to simulate a real BGP router
- Connect with border routers by BGP peering
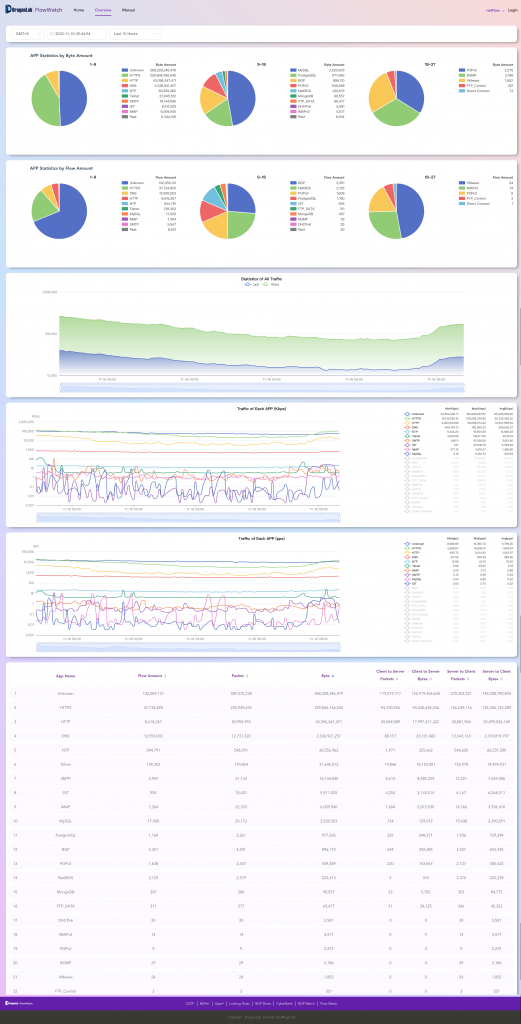
FlowWatch is a passive traffic measurement and analysis system, which can identify the protocol or source application of traffic data by monitoring the original traffic data and extracting IP, port and other information. At the same time, it aggregates the information, and displays the statistical results.
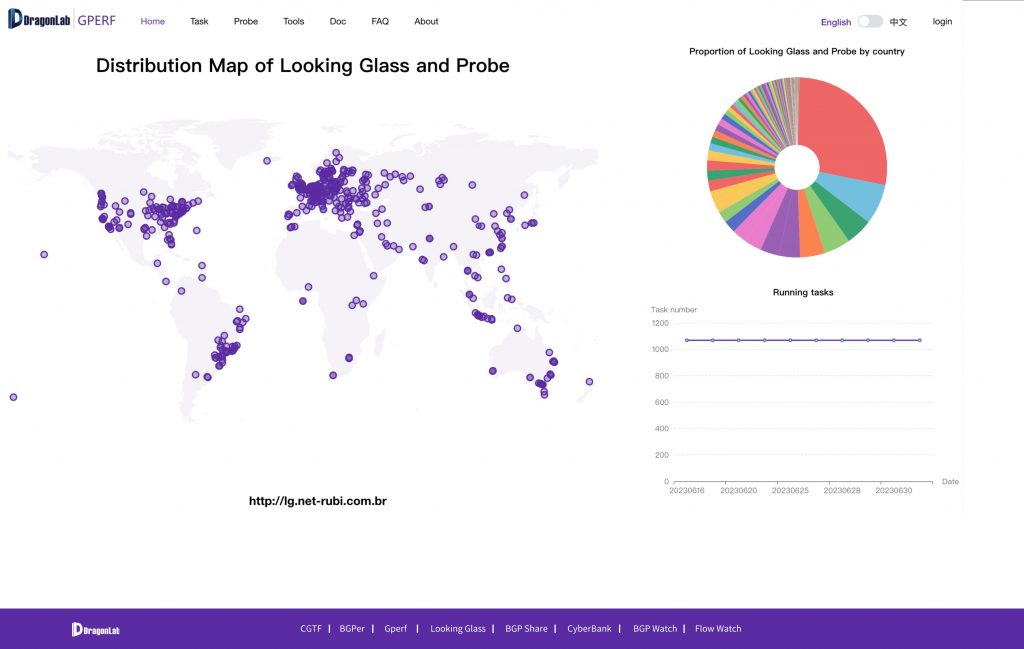
Gperf